7 tips for HR to detect insider threats

Insider threats are a growing concern for organizations worldwide. They come from individuals within the organization, such as employees, contractors or business associates, who have inside information concerning security practices, data and computer systems.
Because these threats come from inside the organization, they are difficult to detect and defend against. However, HR teams have a unique perspective on the organization, making them well-equipped to detect insider threats.
Psychology behind insider threats
To best identify and detect potential insider threats, it helps to understand why employees turn to this method of attack.
The most direct psychological triggers come from personal motivations. This can range from financial incentives and a desire for economic gain to seeking revenge due to perceived wrongs. Some insiders are also driven by ego or the thrill of breaching systems to prove their capabilities.
Ideological and ethical beliefs
Certain insiders may act based on deeply held beliefs, and political or religious ideologies might motivate them to harm your organization. In some cases, they act because they genuinely believe they are serving a greater cause, even if it’s detrimental to the organization.
Many insiders rationalize their actions to alleviate feelings of guilt or wrongdoing. This is due to cognitive biases — they may minimize the harm they’re causing, displace blame or exhibit overconfidence in their actions and the perceived lack of consequences.
Social influences and group dynamics
External entities like competitors or foreign powers may manipulate insiders to extract information about your company. Moreover, group dynamics within the organization can also sway an individual’s actions, especially if they feel supported or pressured by their peers.
The environment within an organization greatly influences behavior. In places with weak security cultures or ambiguous policies, employees may need to grasp the implications of their actions. Over time, they may become desensitized to policy violations and feel more emboldened to commit violations themselves.
Emotional state and personal stressors
Employees facing personal stresses, such as family issues, mental health challenges or other external pressures, might act irrationally. Job dissatisfaction and feelings of being undervalued can also contribute to negative actions.
Rational Choice Theory posits that individuals weigh benefits against risks. If the perceived value of information or potential gain is high and the risk of getting caught is low, an insider might be more inclined to exploit their position.
Unintentional threats and oversights
It’s essential to understand that not all insider threats are malicious. Some employees may inadvertently pose risks due to lack of training, unawareness or simple human errors. Their actions, although unintentional, can still have profound implications.
With the psychology behind insider threats in mind, what behavior does an insider employee typically exhibit?
7 warning signs of insider threats
Companies must stay vigilant to detect insider threats as early as possible and avoid getting compromised. Look out for these common employee behaviors:
- Work behavior and access patterns: One of the primary warning signs of potential insider threats is anomalies in work behavior. Employees accessing systems outside of regular work hours or attempting unauthorized access can be cause for concern. Additionally, consistent remote access at odd times without a clear reason is suspicious.
- Data management concerns: Massive and unusual data transfers, especially to external devices or locations, can indicate potential data theft. Any activity that sidesteps or blatantly violates company protocols on data management needs careful attention.
- Job performance and role changes: A sudden decline in an employee’s job performance might indicate distractions or other motives. Similarly, rapid switches between roles or departments without clear justification can suggest attempts to gain wider, potentially harmful access.
- Personal dissatisfaction and behavioral signs: Vocal dissatisfaction with the company, management or policies can be precursors to malicious intent. Moreover, behavioral changes such as heightened stress, disengagement from tasks or increased isolation from colleagues might signal a potential threat.
- Reactions to oversight and audit: Defensiveness or overreactions to routine checks, security measures or audit processes can be red flags. This behavior can suggest the individual has something to hide or participated in activities they shouldn’t have.
- Financial and external pressures: Employees experiencing severe financial distress might be more prone to insider threats, as they could be more susceptible to bribes or the lure of selling proprietary information. Similarly, unexplained contacts with competitors or overseas entities, especially from countries known for industrial espionage, warrant scrutiny.
- Interpersonal conflicts and restricted interests: Constant confrontations with peers, especially about data or security matters, indicate underlying issues. Likewise, an undue interest in restricted areas should raise concerns.
While all of these can be indicators of insider threats, it is also crucial to note that an employee exhibiting one or more of these behaviors is not necessarily an insider threat.
Address potential insider threats
If massive, reputable companies like Facebook’s WhatsApp — which saw 1.5 billion accounts compromised — can fall victim to data breaches, any company can. Monitoring changes in employee behavior is one of the best ways to detect potential insider threats. If you notice employees exhibiting these insider threat indicators, your HR team has a few ways to resolve the situation.
Robust training and protocols
Companies should conduct regular training sessions to prevent insider threats. Employees should be well-educated about data security and there should be continuous awareness campaigns about the risks and signs of insider threats.
Creating a culture of trust and security is essential, with employees actively encouraged to report any suspicious activities they come across. Promoting a whistleblowing culture where employees feel protected when they report suspicious activities is essential. Ensuring these whistleblowers face no retaliation is a key component in building trust and security.
Every organization should have a clear and concise policy regarding insider threats. These policies should be regularly communicated to employees and they should be well aware of the repercussions of any violations.
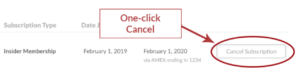
When you terminate an employee or they resign, strict offboarding protocols should be in place. Immediate revocation of all access and conducting thorough exit interviews can prevent potential threats.
Collaboration with IT
HR needs to work closely with the IT department, notifying them of any potential threats. The IT team can be instrumental in monitoring for potential threats, providing critical data and suggesting tools and methodologies to improve security.
Data Loss Prevention (DLP) tools are a technological solution to detect and prevent unauthorized data transfers. Working with IT to implement these can add an extra layer of security.
Remember that while monitoring and vigilance are essential, it’s crucial to respect employee privacy. Striking a balance ensures that while the organization remains secure, the trust and morale of employees aren’t compromised.
Provide support
Understanding the underlying motivations behind insider threats is key to prevention. Whether it’s financial gain, personal grievances, ideological reasons or external influences, grasping these motives can offer valuable insights.
Maintaining open channels for employees to voice concerns, frustrations or issues is invaluable. It allows the company to address potential grievances before they escalate into security concerns.
Insider threats can stem from personal issues. Offering support systems such as counseling can improve overall employee health and deter potential threats.
Multi-faceted approach to security
Whether intentional or inadvertent, insider threats pose a unique challenge to organizations, largely because they emanate from individuals with legitimate access to the system. Their actions, driven by a myriad of psychological, social and environmental factors, can significantly jeopardize the security and integrity of an organization’s assets. Sometimes, the most seemingly innocuous oversight or unintentional error can lead to significant breaches.
Vigilance entails continuous training, fostering a culture of security awareness, ensuring clear communication and routinely evaluating and updating security protocols. Proactive attention and a holistic understanding of insider threats are the cornerstones of robust protection.
Free Training & Resources
Webinars
Provided by Paycom

Resources
Premium Articles
What Would You Do?
Premium Articles