How to Reduce Cybersecurity Risks in Remote Onboarding

A new hire could be a company’s next security risk.
Today’s remote onboarding introduces unfamiliar devices and home networks into organizations, along with urgent paperwork, fast-paced communication and limited in-person contact. While IT handles the technical defenses, HR is the first line of protection.
The way an employer sets expectations and procedures during remote onboarding can either reduce risk or create a costly vulnerability.
Remote Onboarding Threats: The 2025 Reality Check
Attackers now specifically hunt for weak spots during remote onboarding because they know it’s a time of confusion and high activity.
Nearly 80% of organizations faced at least one remote-work security incident in 2025, and breaches tied to remote access cost an average of $4.56 million per hit. Home offices amplify exposure. New employees often use personal Wi-Fi routers and shared devices, phones for logging in and public cloud storage without clear guidelines.
The human factor remains the softest target. A 2023 analysis found negligence or carelessness triggered 98% of reported security breaches, often through reused passwords or hasty link clicks. Technical complexity adds another risk layer — 40% of breaches now involve data spread across multiple environments, and public cloud breaches average $5.17 million in losses.
Hornetsecurity’s 2024 review of 55 billion messages confirmed phishing as the top attack method. Impostors often mimic DHL, FedEx or DocuSign during contract exchanges, luring recruits while they rush through remote onboarding paperwork.
Meanwhile, when workers carry company laptops home, they leave behind the office internet proxy, traffic filters and other protections built into the workplace. That means remote onboarding isn’t just about productivity — it’s about early-stage protection.
Attackers understand this perfect storm of hurried sign-ups, relaxed guardrails and overlapping clouds. HR teams, in partnership with IT, must respond with layered defenses that start when an offer letter goes out.
10 Tactics That Lock Down Remote Onboarding
These strategies are designed to shield organizations without overwhelming new hires or HR teams. They work whether remote onboarding a single employee or scaling a class of new remote workers.
1. Ship Zero-Trust Starter Kits
Partner with IT to send laptops that are already set up with strong protection — such as full-disk encryption, endpoint detection and response, and hardware-based multifactor authentication. The laptop comes in tamper-evident packaging, with a welcome note and simple steps like “Connect to Wi-Fi, then open this page.”
This is framed as a white-glove experience, not a restriction. Security becomes a convenience and not a burden.
2. Verify Identity with Live Proofing
A short video call replaces the old “email us a photo of your driver’s license” routine.
During remote onboarding, the recruiter asks the hire to show government ID next to the laptop’s serial number while a help-desk agent takes screenshots for the file. Moments later, IT captures verification in the background and sends out a secure FIDO hardware key to prevent password reuse immediately afterward.
3. Help New Employees Secure Their Home Network
Rather than instructing employees on how to tweak their routers, provide simple security upgrades, like a one-click app or small plug-in device that automatically routes traffic through company protections using Secure Access Service Edge (SASE).
For HR, this protects sensitive information like Social Security numbers or tax forms without asking the employee to become a home IT expert.
4. Delay Account Access Until Day One
By linking an applicant tracking system with identity and access management APIs, accounts activate only when HR marks the start date. Role-based access controls which systems are visible — just enough for orientation.
After the first week, the system prompts managers to remove unused access automatically. This helps HR eliminate zombie accounts that otherwise stay active indefinitely, which is one of the most overlooked security gaps.
5. Secure Digital Paperwork Against Phishers
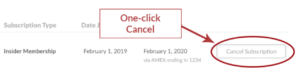
Move offer letters, tax forms and policy sign-offs through DocuSign or a similar platform. Force single sign-on, block email forwarding and wrap every link with real-time scanning.
Add a visual cue like “Only sign forms with this lock icon,” so employees quickly learn to spot fake links. Because this advice shows up in context, not buried in an email, it becomes part of their muscle memory.
6. Check Device Health Before the First Login
Set up rules that confirm the device is safe before allowing sign-in, like checking for patched operating systems, active EDR and encrypted disks the instant a user hits “sign in.” If something fails, a friendly wizard can explain how to fix the issue rather than throwing a cryptic error.
New hires feel guided, not punished, while HR ensures their access doesn’t create a gap in data protection practices.
7. Train with Real-World Phishing Tests
During the first week of remote onboarding, send harmless emails that resemble real phishing attempts, such as a delivery update or benefits reminder.
If a new hire clicks, they’re directed to a quick one-minute training video. It’s not about shame; it’s about setting the tone early that awareness is part of company culture.
8. Automate Offboarding on Background-Check Failure
Most checks will pass, but when one doesn’t, a single API response can trigger instant credential revocation, wipe mobile access and email a prepaid shipping label for device return. The process takes minutes and leaves an audit trail for compliance teams.
This removes the burden from HR during offboarding and avoids awkward manual steps in high-stakes moments.
9. Watch Where Sensitive Data Lives
Data loss prevention may auto-attach labels to every folder that stores personal information or intellectual property. Cloud security posture management flags open folders, sharing mistakes or misused tools.
HR receives only the red flags, so the team doesn’t waste time sorting through safe items. It’s a subtle but powerful way to safeguard employee privacy without constant oversight.
10. Schedule Regular Security Checkups
One month in, the new hire, their manager and an IT specialist should spend 15 minutes reviewing access logs and device health. The IT expert may remove dormant accounts on the spot, while the new employee has a chance to ask technical questions.
This short meeting reinforces that security is a shared responsibility and gives teams honest feedback to improve the next remote onboarding cycle.
Together, these people-focused strategies block common attack paths without drowning newcomers in technical details. Security stays strong, the welcome feels warm, and HR can confidently say every remote hire starts on the right foot.
First-Day Security Shapes Long-Term Culture
HR is responsible for creating a seamless candidate experience, while IT owns the technical enforcement. When both teams meet during hiring surges, they identify gaps.
Shared dashboards showing onboarding ticket counts, phishing-simulation scores and device-health metrics keep everyone focused on measurable outcomes rather than finger-pointing. New hires should feel protected, not policed.
By investing in thoughtful remote onboarding experiences that combine security and support, companies avoid future incidents while showing new employees they’re trusted and protected from day one.
Free Training & Resources
Webinars
Provided by InComm
Webinars
Provided by Mitratech

Resources
The Cost of Noncompliance
You Be the Judge
Premium Articles